Bug sweeping, also known as Technical Surveillance Counter Measures (TSCM), is the process of detecting, locating, and neutralizing covert listening devices and other technical surveillance threats. Bug sweeping is often used by businesses and individuals who are concerned about the possibility of espionage or other malicious activity.
TSCM practitioners use a variety of tools and techniques to detect and locate hidden listening devices, including radio frequency (RF) detectors, thermal imagers, and acoustic detectors. Once a listening device is found, TSCM specialists can neutralize the threat by removing the device, Jamming the signal, or using other countermeasures.
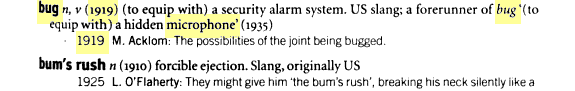
Why people call TSCM “Bug Sweeping” services, is a topic of debate, but one theory is that the term dates back to World War One. The word “Bug” made its first appearance in 1919: (to Equip with) a security alarm system. US slang: a forerunner of bug ‘(to equip with) a hidden microphone’. Src: 20th Century Words
The word “Bugging” became popularized during the Cold War era, when the US and Soviet Union were engaged in a “bug war” where each side would try to plant listening devices in the other’s embassies and other locations. The term “bug” was used to describe these devices, and “sweeping” was used to describe the process of trying to find and remove them. A famous incident was The Great Seal of 1945. In 1945, a group of Soviet children visited the US Embassy in Moscow and gave the Ambassador a hand-carved Great Seal of the US. It stayed in his office until 1952… when technicians discovered a remarkable listening device inside.
Nowadays, the threat of electronic surveillance is not limited to nation states, but extends to criminals, hackers, and other malicious actors who may use listening devices to eavesdrop on private conversations or steal sensitive information. As a result, bug sweeping has become an important security measure for businesses and individuals who are concerned about the possibility of espionage or other malicious activity.
TSCM specialists are often employed by corporations, government agencies, and private individuals to conduct sweeps of their offices, homes, and vehicles. Bug sweeping can be an important part of physical security and is often used in conjunction with other security measures such as access control, CCTV, and perimeter security.
What type of equipment do TSCM specialist use?
TSCM practitioners use a variety of tools and techniques to detect and locate hidden listening devices, including radio frequency (RF) detectors, thermal imagers, acoustic detectors, GSM & 3G Signal Detectors, Cable Checkers, Hidden Camera Detection Devices, and more. There are a number of other devices that are used by TSCM specialists, this article is here to serve as an introduction to what TSCM is and how it works.
RF detectors are handheld devices that can be used to scan an area for radiofrequency signals that may be coming from a hidden listening device. RF detectors can be tuned to specific frequencies, or they can be set to scan a wide range of frequencies.
Thermal imagers are infrared cameras that can be used to detect heat signatures that may be coming from a hidden electronic device. Thermal imagers can be used to detect devices that are turned off but still emitting heat.
Acoustic detectors are microphones that can be used to listen for sounds that may be coming from a hidden listening device. Acoustic detectors can be used to detect devices that are turned off but still making noise, as well as devices that are turned on and emitting RF signals.
GSM & 3G Signal Detectors help discover and identify mobile phone-based devices emitting transmissions, such as cellphones, vehicle trackers, GSM listening devices (bugs), and covert wireless 3G cameras. It may be used in secure meeting rooms to detect hidden GSM bugs and 3G wireless devices (cameras or microphones), unauthorized use of phones in businesses, hospitals, or prisons.
Cable Checkers are highly sensitive audio frequency amplifiers that allow a specialist to hear low audio frequencies. They provide the user with an efficient device that searches for microphones and other bugging signals at extremely low levels ranging from picowatts to volts on all types of cables, in addition to the ability to detect low-voltage audio signals and pulses on any type of wire.
Hidden Camera Detection Devices can be used to find pinhole cameras, wireless hidden cameras, spy cams, and other types of concealed surveillance equipment. These devices can use a variety of methods to detect hidden cameras, including RF detection, optical detection, and acoustic detection.
How do TSCM specialist neutralize the threat?
Once a listening device is found, TSCM specialists can neutralize the threat by removing the device, jamming the signal, or using other countermeasures.
Removing the device is the simplest and most effective way to neutralize a hidden listening device. This can be done by physically locating and removing the device, or by using a device that emits a signal that disrupts the connection between the listening device and its transmitter.
Jamming the signal is another way to neutralize a hidden listening device. This can be done by using a device that emits a signal that disrupts the connection between the listening device and its transmitter.
Other countermeasures that can be used to neutralize a hidden listening device include:
- Physically destroying the device
- Disrupting the power supply to the device
- Shielding the device from electromagnetic signals
- Blocking the transmission path between the device and its transmitter
What do you do if you find a Bug Listening Device?
If you’re having an important meeting, and you find a hidden listening device, STOP and reschedule the event. Then contact a TSCM specialist. They are trained to safely remove and neutralize hidden listening devices. They will also be able to help you determine how the device was placed and who might have placed it. Lastly, they can help you identify vulnerabilities in your security that might have allowed someone to bug your home or office.






